hymaris offers innovative solutions to help your business thrive. Our technology is able to protect your supply chain against a wide range of threats.
Thymaris is bases it’s decisions on the fact that each product is having individual properties which cannot be replicated even by it’s manufacturer. This makes the technology inherently safe and unfakeable
The core judgments are performed through mathematical algorithms which give robust results without room for interpretation. This means that hallucinations cannot appear.
Thymaris is ahead of its time which was approved by multiple patent offices around the globe. This ensures a pristine protection of customer supply chains and IP.
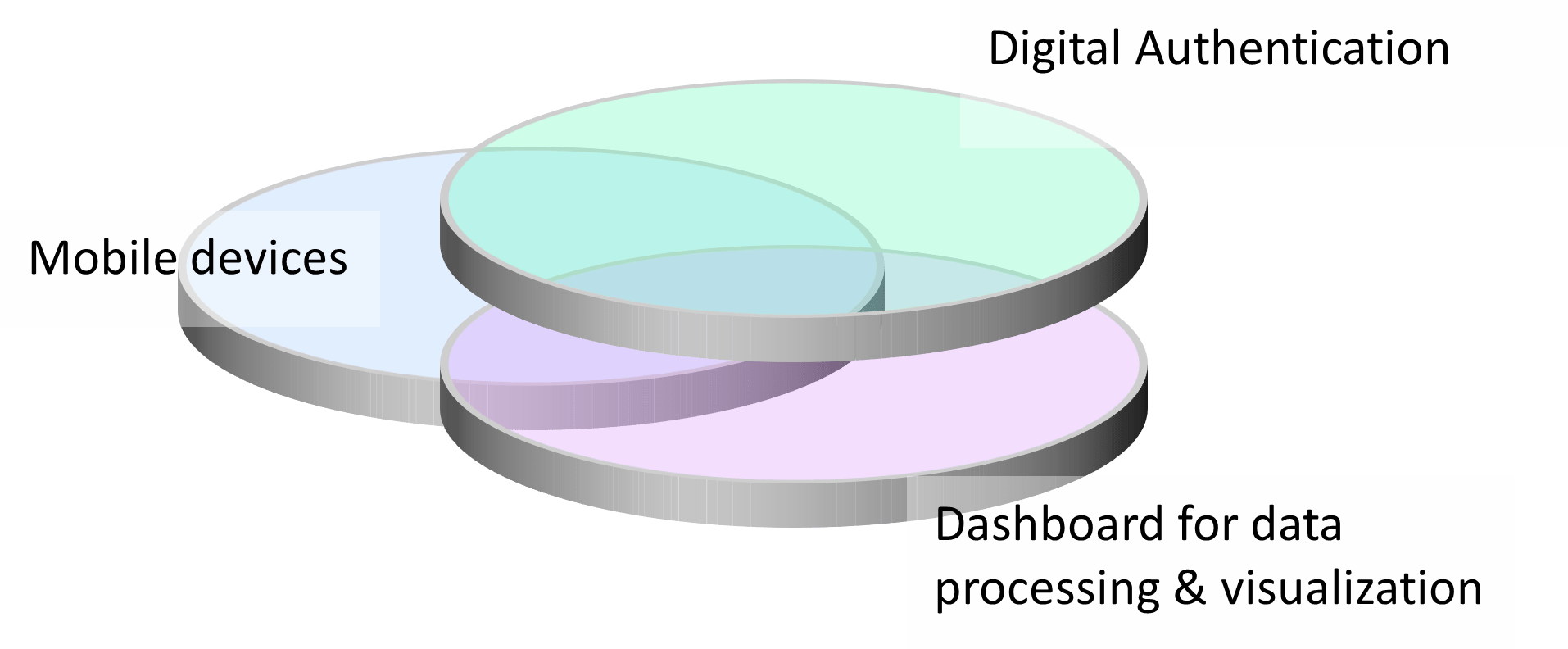
Mobile devices: Nowadays, most standard smartphones offer sufficient performance to support authentication processes in the Thymaris framework. No additional hardware gimmicks are needed. Depending on the Thymaris system configuration, the following options are available:
Digital Authentication technology: To ensure authentication functionality on highest level, Thymaris generate for each item an individual security feature, mostly based on unique printing tolerances (random imperfections) which cannot be reverse engineered. To link such unique security feature to the correlated item, needed for authentication, each one must carry an individual serial number, normally encrypted in a 2D barcode (so called serialized products). The beauty of Thymaris is the fact, that the authentication feature is integrated into the serialization barcode. This allows reading barcode for Track & Trace information and simultaneously authenticating the original provenance of the inspected item.
Dashboard for data processing & visualization: A powerful authentication technology is a prerequisite for a paramount product protection landscape. However, it has to be embedded in a process allowing to monitor scanning activities, validating scanning results. Thymaris system offers a powerful dashboard, allowing easy managing of activities and documenting data. Like a spider at the center of its web, it serves as the central switchboard for all critical system information and the control hub for decisions and actions. Incoming data are triaged, correlated, and—when necessary—manually inspected. Finally, all findings are used for clustering data to identified illicit organizations as a base for additional criminal investigation and involving authorities and launching prosecution.

Bulk Product can be transported in bags which may compromise readability of marks.
Thymaris can withstand even rough treatment to a high degree.

Thymaris is using a scale out architecture (big Data) to handle billions of products
The solution can get data from an individual product in split seconds